Network Routing and Switching Take-home exam
TEN SHORT ANSWER QUESTIONS
Answer all 10 questions from this part.
Each Question is worth 2 marks (10 x 2 = 20 marks).
Question 1 2 Marks/
A block of addresses has the mask /26. If the organization creates 4 equal-sized subnets, how many addresses (including the special addresses) are available in each subnet? Show your calculations.
Answer:
| 16 addresses in each subnet. Total Host=56 Total Special Address= 8 |
Calculations:
| Total Number of Address=2^6=64 Subnet= 64/4=16 Total Host=14*4=56 Total Special Address= 2*4=8 |
Question 2 2 Marks/
A valid classful address was given as 190.53.13.3. What is the default mask for this address?
Answer:
| Since the address lies in class B it must be 16 bits in total which represents the host bit and total addresses per network are 2^16=65,536 in total. Thus, the default mask in CIDR format of the given IP address is /16 and dot-decimal notation 255.255.0.0. |
Question 3 2 Marks/
Given the classless address 215.150.68.112/25, what is the direct broadcast address? Show your calculations (essential).
Answer:
| The direct-broadcast address for 215.150.68.112/25 is 215.150.68.127/25 |
Calculations:
| Number of addresses= 2^7=128 We have to find the binary of the address We have to carry out OR operation by using 1’s complement of the 1’s So we get 215.150.68.112 11010111.10010110.01000100.01110000 00000000.00000000.00000000.01111111 OR operation t11010111.10010110.01000100.01111111 à 215.150.68.127 |
Question 4 2 Marks/
In an IPv4 Header, the value of the Header Length field was decimal 7. What is the total length of the Header in bytes? Explain your answer or show your calculations.
Answer:
| If Header length field was 7 Total Length of the header in bytes= header length*4=7*4=28. So, the total length of the header in bytes is 28. |
Question 5 2 Marks/
Answer:
| This packet is travelling from client to server |
Question 6 2 Marks/
Consider the mask 255.255.254.0. Is this the mask of a classful address, a classless address, an IPv6 address, or a limited broadcast? Give reasons for your choice as well as reasons why the others are not correct.
Answer:
| It is a classless address because the subnet mask can be changed but other address are fixed. |
Question 7 2 Marks/
In your own words, when browsers need to locate a website, briefly explain what information they need from DNS servers.
Answer:
| When a domain name is typed on our browser it checks the cache of the computer to match DNS records that we have entered, if it finds it requests the page from the website host. If there is no record, our request goes to recursive DNS that have been set probably by our ISP, If they have the record cached, result is taken from them and the page is loaded, if the page is still not found it goes to the Root DNS server and ask to find correct top level DNS servers, after finding the piece of information for us located at Authoritative name servers, which provide us the information, finally, the result is cached by recursive DNS servers and by our system and the page is loaded. This is how we get what we are looking for. References DNS Explained – How Your Browser Finds Websites. (2020). Retrieved 18 June 2020, from https://scotch.io/tutorials/dns-explained-how-your-browser-finds-websites |
Question 8 2 Marks/
Answer:
| When the destination is not on a directly attached IP network, it forces the sender to forward the datagram to a router for delivery, indirect routing takes place. In this delivery the packet travels from different router until it finds the one that is connected to the same physical network as its destination. References (2020). Retrieved 18 June 2020, from https://www.docsity.com/en/answers/what-is-the-difference-between-direct-and-indirect-delivery/113302/#:~:text=In%20a%20direct%20delivery%2C%20the,network%20as%20its%20final%20destination.%22 IBM Knowledge Center Error. (2020). Retrieved 18 June 2020, from https://www.ibm.com/support/knowledgecenter/SSLTBW_2.4.0/com.ibm.zos.v2r4.hald001/indirect.htm |
Question 9 2 Marks/
Classful addressing was referred to as “two-level addressing”. Briefly explain the two levels referred to.
Answer:
| Eventhough all the networks belong to a single block, each address in classful addressing contains two parts that is netid and hostid. The netid defines the network where as hostid defines a host connected to that network. The n bits in the class defines the net whereas 32-n defines the host. The value of n however depends on the class the block belongs to for class A n is 8 for class b n is 16 and for class C n is 24. References khadum Idrees, D. (2020). Two level addressing. Retrieved 18 June 2020, from http://www.uobabylon.edu.iq/eprints/publication_1_23319_300.pdf |
Question 10 2 Marks/
Enabling Options in IPv4 changes the header length but enabling Options in IPv6 does not change the header length. Briefly explain the reason for this difference.
Answer:
| IPv6 incorporates an improved alternative component over IPv4. IPv6 choices are set in independent augmentation headers that are situated between the IPv6 header and the transport layer header in a parcel. Most IPv6 expansion headers are not analyzed or handled by any switch along a parcel’s conveyance way until the bundle shows up at its last goal. This element is a significant improvement in switch execution for parcels that contain choices. In IPv4, the nearness of any alternatives requires the switch to analyze all choices. Dissimilar to IPv4 alternatives, IPv6 augmentation headers can be of discretionary length. Likewise, the quantity of alternatives that a parcel conveys are not constrained to 40 bytes. This component, in addition to the way in which IPv6 choices are handled, licenses IPv6 choices to be utilized for capacities that are not reasonable in IPv4. A genuine case of IPv6 alternatives is the IPv6 confirmation and security embodiment choices. To improve execution when dealing with ensuing alternative headers, and the transport layer that follows, IPv6 choices are consistently a whole number different of eight octets in length. The number various of eight octets holds the arrangement of ensuing headers. |
End of Part A
Question 1 5 Marks/
The ABEL Company has requested a block of IP addresses from an ISP. The block that was allocated to ABEL included the address 191.56.125.34/25.
Calculate the number of addresses in this block, the network address, the direct broadcast address, and the range of addresses that would be available for use by hosts.
The number of addresses available in this block: (1 mark/ )
| 128 |
The network address: (1 mark/ )
| 191.56.125.0 |
The direct broadcast address: (1 mark/ )
The range of addresses that can be used by hosts: (1 mark/ )
| From:_191.56.125.1____ to: 191.56.125.126____ |
Calculations: (1 mark/ )
| 10111111.00011100.01111101.00100010 11111111.11111111.11111111.10000000 AND operation 10111111.00011100.01111101.00000000à Network Address 191.56.125.0 10111111.00011100.01111101.00100010 00000000.00000000.00000000.01111111 OR operation ——————————————————– 10111111.00011100.01111101.01111111àlast address broadcast address. 191.56.125.127 |
Question 2 5 Marks/
A company has been granted a block of classless addresses which starts at 198.87.24.0/23. Create the following 4 subnets by calculating the subnet address including the prefix for each of the following subnets. Create a table to organise your answer. Show your working in the space provided.
- 1 subnet with 128 addresses
- 1 subnet with 64 addresses
- 2 subnets with 32 addresses each
Answer:
| Subnet Address No of Address needed No of Address allocation Net Bit/Prefix Subnet bit Host bit Mask 198.87.24.0 – – 23 0 9 23 198.87.24.128 128 128 23 2 7 26 198.87.24.192 64 64 23 3 6 27 198.87.24.224 32 32 23 4 5 27 |
Calculations:
| 198.87.24.0/23 Number of Address= 2^9=512 We have to find 1 subnet with 128bit address We need to keep 7bit in the host bit so the mask will be 32-7=25 198.87.24.0/25 (128 address starting from 0 to 127) We need to keep 6bit in the host bit so the bit mask will be 32-6=26 198.87.24.128/26 (64 address starting from 128 to 191) We need to keep 5bit in the host bit so the bit mask will be 32-5=27 198. 198.87.24.192/27 (32 address starting from 192 to 223) 198.87.24.224/27 (32 address starting from 224 to 255) In the above table Subnet bit= 32- (Net bit +Host bit) |
Scroll down to the next question
Question 3 5 Marks/
Briefly explain how CWND and TCP memory buffers work together to control flow and congestion issues.
Answer:
| Congestion Window (CWND) is a TCP state variable that restricts the measure of information the TCP can send into the system before getting an acknowledgment. The Receiver Window (RWND) publicizes the measure of information that the goal side can get. Together, the two factors are utilized to manage information stream in TCP associations, limit blockage, and improve organized execution. Congestion in Network can happen when bundles sent from the source (the server) surpass what destination can deal with (the client). At the point when the buffers get topped off at the destination, the parcels are incidentally put away in cushions at both the source and goal as they hold back to be sent to the upper layers which prompt congestion and cause bundle misfortune, retransmissions, diminished information throughput, execution debasement, and even system breakdown in outrageous cases. TCP utilizes congestion window and the recipient window to control and stay away from organize blockage. The measure of information that can be transmitted through a TCP association is reliant on the congestion window, which is kept up by the source and recipient window is kept up by destination. The destination demonstrates the size of the recipient window through the TCP header. This publicizes the measure of information that it can get and empowers the blockage window to decide the measure of information it can dependably transmit without an ACK. When gotten, the information is put away in the buffer and the receiver sends an ACK or a lot of ACKs relying upon the measure of got information. The congestion window size keeps expanding up to the most extreme recipient window, or until the system arrives at its breaking point. The pace of sending information is bound to the congestion window, and in any event, when the reciever window is huge, the congestion window might be smaller – particularly if the system doesn’t bolster transmitting information identical to the most extreme RWND size. Congestion is distinguished either by receipt of a copy affirmation or a timeout signal. When this occurs, the TCP sender diminishes the send rate by diminishing the congestion window size by a factor controlled by the calculation utilized. The most extreme measure of unacknowledged information that the source can send is the lower of the two windows. Reference Jhonson, J. (2017). What is CWND and RWND? – Articles for Developers Building High Performance Systems. Retrieved 18 June 2020, from https://blog.stackpath.com/glossary-cwnd-and-rwnd/ |
Scroll down for the next question
Question 4 5 Marks/
The section of the Internet in the diagram below shows six networks and four routers, labelled R1, R2, R3 and R4. Construct the routing table of router R3 by completing the table provided below the diagram. List the networks in longest mask order.
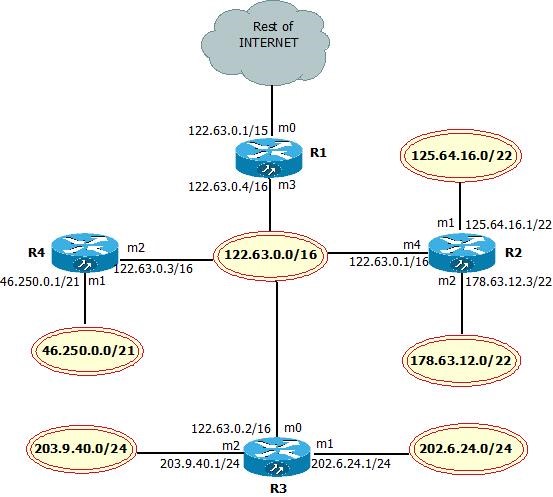
| Prefix | Mask | Network address | Next-hop address | Interface |
| /24 | 255.255.255.0 | 203.9.40.0 | ———- | M2 |
| /24 | 255.255.255.0 | 202.6.24.0 | ———— | M1 |
| /22 | 255.255.252.0 | 178.63.12.0 | 122.63.0.1 | M0 |
| /22 | 255.255.252.0 | 125.64.16.0 | 122.63.0.1 | M0 |
| /21 | 255.255.248.0 | 46.250.0.0 | 122.63.0.3 | M0 |
| /16 | 255.255.0.0 | 122.63.0.0 | ————– | M0 |
| Default | 0.0.0. | Default | 122.63.0.4 | M0 |
Question 5
Discuss how classful address blocks allocated to organizations may result in wastage of IP addresses; in addition, explain how the techniques of subnetting and supernetting help organisations to alleviate the problems referred to.
Answer:
| There are numerous systems that have more than the 254 hosts given by a Class C address, and there are none that have the 16 million gave by a Class A. The classful IP tending to framework, in this manner, end up being inefficient as the IP address space became swarmed. CIDR is a subnetting strategy that empowers directors to put the division between the system bits and the host bits anyplace in the location, not simply between octets. This makes it conceivable to make systems of practically any size. CIDR additionally presented another documentation for arrange addresses. A standard IPv4 arrange address is trailed by a forward slice and a numeral indicating the size of the system identifier. For instance, 192.168.43.0/24 speaks to a location that utilizes a 24-piece organized identifier, leaving the other 8 bits for up to 254 host identifiers, which would once in the past be known as a Class C address. CIDR permits switches to total, or sum up, directing data. It does this by utilizing a bit cover rather than a location class to decide the system segment of a location. This contract the size of the directing tables utilized by the switch. At the end of the day, only one location and cover mix can speak to the courses to numerous systems. Without CIDR and course total, a switch must keep up numerous individual passages for the courses inside a similar system, rather than one course for that specific system when utilizing CIDR tending to. Super netting utilizes a piece veil to bunch various classful systems as a solitary arrange address. Super netting and course collection are various names for a similar procedure. Notwithstanding, the term supernetting is frequently applied when the collection systems are under basic authoritative control. Supernetting takes bits from the system bit of the system veil, while subnetting takes bits from the host bit of the subnet cover. Super netting and course collection are basically the opposite of subnetting. References Zacker, C. (2020). CompTIA Network+ Rapid Review: Network Concepts | Microsoft Press Store. Retrieved 19 June 2020, from https://www.microsoftpressstore.com/articles/article.aspx?p=2201313&seqNum=3 |
Scroll down for PART C
PART c
THREE LONG ANSWER QUESTIONS
Answer the following 3 questions in a maximum of one page per question.
Type your answers in the spaces provided. The space will expand as you type.
Use your own words.
Question 1
Although IPv6 is now the official standard, what are some of the factors that explain why IPv4 is still the dominant system today despite the supply of IPv4 addresses being officially exhausted?
Answer:
| An Internet Protocol (IP) address is a numerical identifier doled out to every gadget associated with the web. Extensively, IP delivers permit gadgets to converse with one another and trade data. In promotion tech explicitly, IP tends to help geo-target commercials and empower meeting level recurrence topping in treat less conditions. Internet Protocol variant 4 (IPv4) is utilized for most of web traffic today. IPv4 addresses are designed utilizing 32-bits, which means there are a little more than 4 billion remarkable mixes. In 1983, this appeared as though all that anyone could need one-of-a-kind IP addresses. Be that as it may, because of the developing number of web associated gadgets, the American Registry for Internet Numbers (ARIN), reported they had formally come up short on IPv4 addresses. The declaration from ARIN was not amazing. Fully expecting this, the Internet Engineering Task Force (IETF) presented a draft of the IPv6 standard in 1998, which was confirmed into a web standard in July 2017. IPv6 uses 128-bits and offers 340 undecillion (340 trillion, trillion, trillion) remarkable IP addresses. This implies there are all that could possibly be needed remarkable IPv6 addresses accessible for the developing number of web associated gadgets. Today, IPv4 still records for most of web traffic, notwithstanding the lack of extraordinary IP addresses. The proceeded with utilization of IPv4 is made conceivable through the use of Network Address Translation portals, which permit various gadgets associated on a similar system to share a solitary open IPv4 address. The progress from IPv4 to IPv6 will permit every individual gadget to have its own exceptional IP address. From the start, having a one of a kind IP for every gadget may seem like IPv6 offers another constant identifier that can be utilized also to an IFA. In any case, as indicated by Chris Row, frameworks engineer at SpotX that isn’t the situation. “It is a misinterpretation that the expansion in one of a kind IP tends to accessible with IPv6 will permit promoters to utilize IP address as a determined identifier, The IP address for a gadget changes after some time, this change can happen for two or three reasons.” To begin with, IP delivers don’t have a place with the gadgets utilizing them, they are doled out by the system every gadget is associated with. Each time a gadget associates with another system, it is given another IP. Take your PC, for example. Each time you interface with another system at work, at a bistro, or at the air terminal, your gadget is relegated another IP address. Second, Internet Service Providers (ISPs), for the most part appoint dynamic IP addresses. Which means, IP addresses intermittently change, regardless of whether a gadget isn’t interfacing with another system. “As a rule, the change from IPv4 to IPv6 won’t mean much as far as new abilities for promoting, “Similarly as with IPv4, IPv6 takes into consideration geo-focusing on and empowers meeting level recurrence topping for cookieless conditions. The greatest effect is the necessity for distributers and promotion tech sellers to help IPv6.” As of now, SpotX is banded together with a geo-focusing on merchant that bolsters geolocation administrations for IPv6 addresses. There is a conspicuous requirement for IPv6, yet it has seen moderate selection. This is because of different variables, including cost, the unpredictability of relocating from IPv4 to IPv6, and existing workarounds that make it conceivable to delay the update to IPv6. For the reasons over, the change to IPv6 won’t occur incidentally, and IPv4 likely isn’t leaving at any point in the near future. Rather, applications and ISPs will start to offer help for both IP forms, an idea known as double stack support. This takes into account web associated gadgets to convey paying little heed to the IP rendition utilized. In spite of the snags, the change to IPv6 is vital and unavoidable. Without IPv6, client experience would in the long run be affected. Projects would start to back off and gadgets would make some hard memories speaking with one another, affecting things like web speed and administrations like Voice over IP and web conferencing. By and large, the progress to IPv6 is useful for everybody over the long haul; it’s simply going to be a moderate excursion. References O’ Hara, A. (2019). What is IPv6 and why do we need it? – SpotX. Retrieved 19 June 2020, from https://www.spotx.tv/resources/blog/product-pulse/what-is-ipv6-and-why-do-we-need-it/ |
Question2
Briefly explain how IPv6 can co-exist with IPv4 once the adoption of IPv6 becomes more widespread whilst IPv4 is still significant in networking.
Answer:
| The dependence on IP delivers of foundation to control, secure, course, and track everything from basic system housekeeping to agreeing to complex administrative guidelines makes it hard to just “flick a switch” and move from the old type of tending to (IPv4) to the new (IPv6). This dependence is spread here and there the system stack, and ranges foundation as well as the very procedures that keep server farms running easily. Firewall rules, ACLs, contents that mechanize ordinary assignments, directing from layer 2 to layer 7, and application design are probably going to impart utilizing IPv4 addresses. Customers, as well, may not be prepared relying upon their age and working framework, which makes a basic “cut over” system inconceivable or, best case scenario, loaded with the potential for technical backing and business challenges. The contrasts somewhere in the range of IPv4 and IPv6 in tending to are likely the most noticeable and oft-referenced change, as it is the length of the IPv6 address that drastically extends the accessible pool of IP locations and consequently is of the most intrigue. IPv4 IP addresses are 32-bits extended period of time IPv6 addresses are 128-bits in length. However, IPv6 addresses can (and do) interoperate with IPv4 addresses, through an assortment of strategies that permit IPv6 to convey along IPv4 addresses. This is accomplished using IPv4 mapped IPV6 addresses and IPv4 perfect IPv6 addresses. This permits IPv4 addresses to be spoken to in IPv6 addresses. Conventional IPv4 Address – 192.168.0.1 IPv4 Compatible IPv6 Address :192.168.0.1 IPv4 Mapped IPv6 Address: ffff:192.168.0.1 Be that as it may, the genuine disengage somewhere in the range of IPv4 and IPv6 is in the distinctions in their headers. It is these distinctions that cause IPv4 and IPv6 to be contrary. An IPv4 bundle header is a fixed-length, 40 bytes in length. An IPv6 parcel header is variable length and can be up to 60 bytes in length. Conventional IP “alternatives” are conveyed inside the IPv4 header, while in IPv6 these choices are annexed after the header, considering greater adaptability in expanded choices over the long run. These distinctions are centre to the convention and in this manner center to the bundle handling motors that drive most switches and switches. Except if organized foundation is running what is known as a “double stack”, for example, two free systems administration stacks that permit the preparing and ensuing interpretation of the two conventions, the framework can only with significant effort handle both IPv4 and IPv6 simultaneously. This puts forth the assignment of moving a huge attempt, one that most associations have kept on putting off even though the times of IPv4 address accessibility are waning. Master had evaluated that open IPv4 addresses will be exhausted constantly 2012 which makes it basic that specialist organizations, facilitating organizations, and distributed computing suppliers relocate as soon as possible or hazard being not able to offer types of assistance to clients, Less than 10pc still accessible” noticing that there is little driving force for associations to change from IPv4 to IPv6 notwithstanding proceeded with consumption of IPv4 addresses: “IPv4 and IPv6 addresses are not good. It was in fact achievable to make the two sorts of IP address converse with one another, however it would be best for organizations and ISPs to change to IPv6 at the earliest opportunity, to keep systems stable and evade intricacy when IPv4 addresses run out.” Numerous organizations are putting off the change to IPv6 in light of the fact that, in any event, when all open IPv4 addresses have been distributed, they will keep on having the option to dispense private IPv4 addresses inside. Be that as it may, anybody running open confronting sites should make their locales obvious as IPv6 addresses, as their clients will be on IPv6 addresses. References MacVittie, L. (2011). Can IPv4 and IPv6 Coexist? | Data Center Post. Retrieved 19 June 2020, from https://datacenterpost.com/can-ipv4-and-ipv6-coexist/ |
Question 3
Discuss the role that Network Address Translation (NAT) and Port Address Translation (PAT) plays in making internet routing more efficient.
Answer:
| Network Address Translation (NAT) is where a system gadget, typically a firewall, appoints an open location to a PC (or gathering of PCs) inside a private system. NAT restrains the quantity of open IP that tends to an association or organization must use, for both economy and security purposes. Well-known type of system interpretation includes a huge private system utilizing addresses in a private range (10.0.0.0 to 10.255.255.255, 172.16.0.0 to 172.31.255.255, or 192.168.0 0 to 192.168.255.255). The private tending to plot functions admirably for PCs that just need to get to assets inside the system, similar to workstations requiring access to document servers and printers. Switches inside the private system can course traffic between private locations with no difficulty. Notwithstanding, to get to assets outside the system, similar to the Internet, these PCs must have an open location with the goal for reactions to their solicitations to come back to them. This is the place NAT becomes an integral factor. Web demands that require Network Address Translation (NAT) are very intricate yet occur so quickly that the end client once in a while realizes it has happened. A workstation inside a system makes a solicitation to a PC on the Internet. Switches inside the system perceive that the solicitation isn’t for an asset inside the system, so they send the solicitation to the firewall. The firewall sees the solicitation from the PC with the inner IP. It at that point makes a similar solicitation to the Internet utilizing its own open location, and returns the reaction from the Internet asset to the PC inside the private system. From the point of view of the asset on the Internet, it is sending data to the location of the firewall. From the point of view of the workstation, apparently correspondence is straightforwardly with the webpage on the Internet. When NAT is utilized along these lines, all clients inside the private system get to the Internet have a similar open IP address when they utilize the Internet which implies single open locations required for hundreds or even a great many clients. Most current firewalls are stateful – that is, they can set up the association between the inward workstation and the Internet asset as they can monitor the subtleties of the association, similar to ports, parcel request, and the IP tends to included. This is called monitoring the condition of the association. Along these lines, they can monitor the meeting made out of correspondence between the workstation and the firewall, and the firewall with the Internet. At the point when the meeting closes, the firewall disposes of the entirety of the data about the association. There are different utilizations for Network Address Translation (NAT) past just permitting workstations with inward IP delivers to get to the Internet. In huge systems, a few servers may go about as Web servers and require access from the Internet. These servers are doled out open IP addresses on the firewall, permitting people in general to get to the servers just through that IP address. Be that as it may, as an extra layer of security, the firewall goes about as the go between the outside world and the ensured interior system. Extra standards can be included, including which ports can be gotten to at that IP address. Utilizing NAT along these lines permits organize designers to all the more effectively course inside system traffic to similar assets, and permit access to more ports, while limiting access at the firewall. It likewise permits definite logging of interchanges between the system and the outside world. NAT can also be utilized to permit particular access to the outside of the system, as well. Workstations requiring extraordinary access outside the system can be relegated explicit outer IPs utilizing NAT, permitting them to speak with PCs and applications that require an exceptional open IP address. Once more, the firewall goes about as the middle person, and can control the meeting in the two headings, confining port access and conventions. NAT is a significant part of firewall security which monitors the quantity of open tends to utilized inside an association, and it considers stricter control of access to assets on the two sides of the firewall Reference Internet, T. (2019). What is Network Address Translation (NAT)?. Retrieved 19 June 2020, from https://whatismyipaddress.com/nat#:~:text=In%20large%20networks%2C%20some%20servers,require%20access%20from%20the%20Internet.&text=Using%20NAT%20in%20this%20way,restricting%20access%20at%20the%20firewall. |
