<script async src="https://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js?client=ca-pub-4462760071454301"
crossorigin="anonymous"></script>COIT20262 – Advanced Network Security, Term 2, 2020
Assignment 2 Submission
| Due date: | 10 am Monday 12 October 2020 | ASSESSMENT |
| Weighting: | 40% | 2 |
| Length: | N/A |
Student Name:
Student ID:
Campus:
Tutor:
- HTTPS and Certificates
Part (b) Information Learnt
As shown in packet 15 in the capture disk, the port number used by the server was 8080. “Hypertext Transfer Protocol Safe” means HTTPS. HTTPS is the protocol for transmitting encrypted HTTP data via a secure connection. The port number is useful for the attacker as all HTTP requests and contact between the server, and the client workstation can easily be intercepted. This form of HTTP communications and intercepts are the most probable cybersecurity attacker known as “Man in the middle.” It is an assailant who waits on a legal matter as an interchange for grades request on the student’s contact with the server. However, due to the delicate topic of student degrees, the intruder cannot listen to this contact.
It offers protection against man-in-the-medium attacks, and bi-directional data encryption from user-to-network prevents overflow and violence. A trusted third party is required to sign encrypted server-side certificates by the HTTPS authentication feature. HTTPS encryption is achieved in two ways by extension. Only the customer can decrypt the service data. HTTPS encrypts data, protecting against scamming, interference, and data manipulation between the user and the server. The person in the center can control the classes while masking them as an actual student. This attacker can also manage the student’s degrees to depict falls or, at worst, remove student files from the databank or fetches the files, download them and blackmail them.
By configuration HTTPS and certificates , it has been learnt that there are some websites which requires the proper information about security of web application so that HTTPS and SSL certificates are allowed to have an effective working of HTTPs configuration allowed in the core level deployment of information system with secure modelling and execution. It is also managed to have the proper view of implementation in order to get the detailed structure about having the proper information management techniques about having the major concern and view of information as per the proper validation and verification of service level implementation about learning the information management interfaces and their usability analytics.
Part (c) Certificates
| Information | Certificate 1 | Certificate 2 |
| Whose public key is included? | Owner’s public key | Owner’s public key |
| What hash algorithm was used in signing? | The certificate includes information about the key, information about the Signature Algorithm: | Signature Algorithm |
| Whose private key was used when creating the certificate? | CA’s key certificate | CA’s key certificate |
Part (d) CRL and OSCP
OSCP is an ethical hacking credential issued by Offensive Security that teaches penetration-testing methodologies and the Kali Linux delivery tools. OSCP (Offensives Security Certified Professional). The OSCP is a hands-on qualification to insert holders in a secure laboratory setting to assault and penetrate various live machines. It is considered to be more technical than other certificates of ethical hacking and one of the few which requires proof of realistic penetration tests. A CRL is a list of digital certificates that have already been withdrawn and can no longer be trusted by the issuing certificate authority (CA) before their scheduled end date. CRL is the standard test type for validity. A CRL lists withdrawn or no longer available serial certificate numbers. CRLs allow the verifier to verify the revocation status of the certificate during checks. The restricted CRLs shall be 512. CRL is the certification list which has been revoked by CA which is one of the most authentic status protocol (OCSP) – OCSP is a protocol for checking revocation of a single certificate interactively using an online service called an OCSP responder.
Part (e) Validity Period
- The total period is three years (or 39 months) for the validity of DV / OV SSL certificates. The higher the key size, the safer the endorsement is from assailants, however will require additionally preparing to utilize. The more drawn out the legitimacy time frame, the less authentication support required (and possibly some assistance interruption), yet the endorsement is more defenseless against being undermined.
- Key length of 1024:Validity Period = not greater than 6-12 years
- Key length of 2048: Validity period = not greater than 2 years
- Key length of 4096: Validity period = not greater than 16 years
- Wi-Fi Security and Authentication
Part (a) Network Diagram
Part (b) Table of Addresses
Add rows where necessary
| Server | IP Address | Port(s) |
| Web | 207.200.83.29 | 80 |
| Network | 2001:4898:23:1002:20f:1fff:feff:b3a3 | 7022 |
| Mac | 001e.f724.a160 | Fa0/3 |
Part (c) MAC Address Filtering Explanation
An additional layer of validation of MAC addresses is provided by testing the device’s MAC address while refusing an accepted address list. The client is not on the network while the client’s address is in the router list. MAC address filtration should be done by revoking the different useless certificates.
Part (d) MAC Address Filtering Recommendation
You have a specific MAC address on your computer, which can be found on a network. Typically, a router may connect a computer by filtering a MAC Address as long as it knows the passphrase. A router with an authorized MAC address list will first compare the MAC address of machinery. If MAC addresses are expressly accepted, allow a computer to access the Wi-Fi network.
Part (e) WPA2 Personal
It is a way of encrypting the network using WPA2 with the optional Pre-Shared Key (PSK) authentically. It is built with no business authentication service for home users.
Part (f) Centralised Authentication
A single online sign-up protocol is the Key Authentication Service (CAS). Its purpose is to allow users to access various applications only once when providing credentials. It also lets mobile apps authenticate users without the need to provide password authentication keys. CAS also uses this protocol in a software application.
Part (g) Finding password
You can make the changes as below to find :
- Right-click on the Start menu.
- Click on “Network Connections”
- Click on “Network and Sharing Center”
- Click on the name of your Wi-Fi network.
- Click on the “Wireless Properties” button.
- Go to the Security tab.
- Select the “Show Characters” checkbox to reveal your network security key.
Part (h) Recommended Storage of Passwords
As for the default, a few authentication instructions are provided below: at least six characters. There should be no consecutive characters of equality. Do not only use numbers, letters. Letters. Do not delete expired buttons. Ask for daily updates of the passwords.
Part (i) Password Policy
New Users
The new privacy policy governs non-duo account confidentiality. In Pair, an individual registered as a mobile, hardware tacks, etc. with an authentication mechanism.
Changing Passwords
I. The network owner should change the entry password at regular intervals and not reuse the previous passwords.
The advantage of the method: -The intruder will not be able to strike Bruce by force after performing the above operation.
The downside of the method: -Account disable operation will occur at any moment, and modifying the password is an essential task.
II. II. After unsuccessful log-in attempts, the user’s account should be closed.
The benefit of the method: -The attacker will not execute a cyber-attack after performing the above operation.
The downside of the method: -There is a need to include the administration after the account has been disabled.
III. III. The user should stop specifying the personal information of a personal account
The benefit of the method: -The attacker will not execute a cyber-attack after performing the above operation.
The disadvantage of the method: -A ‘forgot password’ could be likely after this procedure has been carried out.
Part (j) Password Plus Token
The token can be created by creating Account, CreateUserAndAccuunt, or GenerePasswordResetToken. The password can be reset with code, but the popular protocol is to provide the user with an E-mail to verify the new toke password (with a token and page connection).
Part (k) Token Only
The token is used besides or instead of a password. It functions as an electronic key to unlock anything.
- Firewalls and iptables
Part (a) Firewall Locations
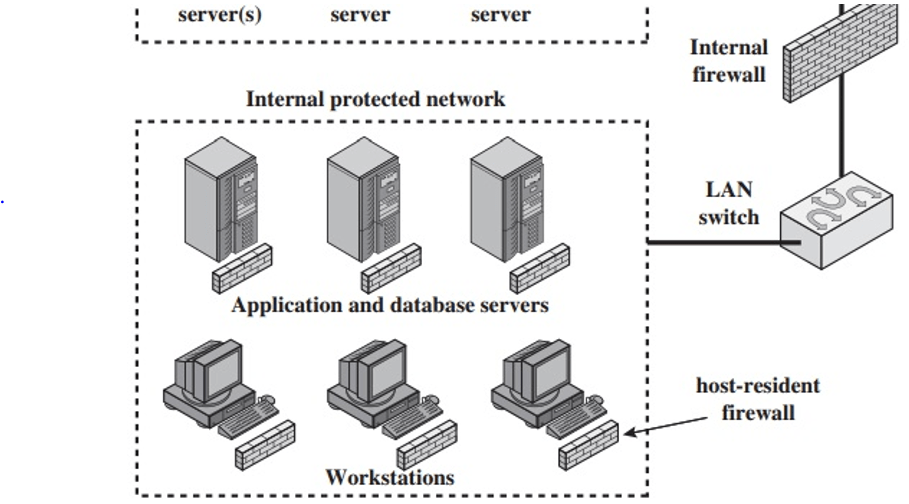
The firewall location includes network-based and host-based
a firewall is situated to give a defensive boundary between an outside, conceivably untrusted wellspring of traffic and an interior organization. Considering that overall rule, a security head must settle on the area and on the quantity of firewalls required. In this segment, we take a gander at some regular choices.
DMZ Networks
An outside firewall is set at the edge of a neighborhood or undertaking organization, simply inside the limit switch that interfaces with the Internet or some wide region organization (WAN). At least one interior firewalls ensure the main part of the enter-prise network. Between these two kinds of firewalls are at least one arranged gadgets in a district alluded to as a DMZ (peaceful area) organization. Frameworks that are remotely available yet need a few insurances are normally situated on DMZ organizations. Regularly, the frameworks in the DMZ require or encourage outside con-nectivity, for example, a corporate Web website, an email worker, or a DNS (area name framework) worker.
The outer firewall gives a proportion of access control and assurance for the DMZ frameworks steady with their requirement for outside network. The outer firewall likewise gives a fundamental degree of insurance for the rest of the undertaking organization. In this sort of design, inner firewalls fill three needs:
1. The interior firewall includes more tough separating capacity, contrasted with the outside firewall, so as to shield endeavor workers and workstations from outer assault.
2. The interior firewall furnishes two-route security as for the DMZ. To start with, the inward firewall shields the rest of the organization from assaults dispatched from DMZ frameworks. Such assaults may start from worms, rootkits, bots, or other malware held up in a DMZ framework. Second, an inside firewall can shield the DMZ frameworks from assault from the inward secured network.
Various interior firewalls can be utilized to shield parts of the inside organization from one another. For instance, firewalls can be designed with the goal that inside workers are shielded from inward workstations and the other way around. A typical practice is to put the DMZ on an alternate organization interface on the outer firewall from that used to get to the inward organizations.
Host-occupant firewall: This classification incorporates individual firewall programming and firewall programming on workers. Such firewalls can be utilized alone or as a component of a top to bottom firewall organization.
• Screening switch: A solitary switch among inward and outside organizations with stateless or full parcel sifting. This course of action is normal for little office/home office (SOHO) applications.
Single stronghold inline: A solitary firewall gadget between an interior and outside switch . The firewall may execute stateful channels and additionally application intermediaries. This is the run of the mill firewall apparatus design for little to medium-sized associations.
• Single stronghold T: Similar to single stronghold inline however has a third organization interface on stronghold to a DMZ where remotely noticeable workers are put. Once more, this is a typical apparatus setup for medium to enormous associations.

• Double stronghold inline: The DMZ is sandwiched between stronghold firewalls. This design is basic for enormous organizations and government associations.
• Double stronghold T: The DMZ is on a different organization interface on the stronghold firewall. This design is likewise regular for enormous organizations and oversee associations and might be required. For instance, this setup is required for Australian government use.
<script async src="https://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js?client=ca-pub-4462760071454301"
crossorigin="anonymous"></script>Part (b) Limitations
• You can’t defend the firewalls from incorrect decisions.
• Firewalls can not enforce policies on passwords or prevent misuse of passwords. In this area, your log-in system is essential, as it specifies appropriate behavior and has implications for non-conformity.
• If your security policy is too weak, firewalls cannot protect you.
.Centralized location.
No outside IP accessibility
Part (c) Firewall Design
Repeat the tables for as many rules as necessary
| Rule | SrcIP | SrcPort | DstIP | DstPort | Protocol | Action |
| 1 | 23.63.0.0 | Any | 10.4.0.0 | Any | TCP | Allow |
Explanation:
The network traffic monitoring points between the switch and router are established through a firewall. It inspects the data packet coming from the transmission system and conducts the packet sort, Internet protocol addresses, and additional information investigations to Accept and reject it. Before the system gateway and between the protected and protecting network, the hardware firewall must be mounted. An external network thus establishes a trustworthy internal network interface.
Requires traffic to any destination from any source. This is the worst form of regulation on access control. It breaches the usual standards of denial of traffic safety and the least correct one.
| Rule | SrcIP | SrcPort | DstIP | DstPort | Protocol | Action |
| 2 | 12.0.0.0/7 | 80 | 10.0.0.0/8 | 443 | UDP | Accept |
There is minimal resource for forwarding
• No replication should be done of the approximate source placement
• the closer partitions are identical
Part (d) iptables
Include the actual iptables rules here, and explain how it relates to your design (including justifying any missing rules)
The Linux-based firewall utility Iptables is exceptionally scalable. There is a way that iptables can be useful for you if you are a novice Linux hacker or a system administrator.
Network Diagram: –
| Rule No | Transport | Source IP | Source Port | Dest IP | Dest Port | Action |
| 1 | TCP | 104.55.0.0 | any | 10.3.3.31 | 22 | Accept |
| 2 | TCP | 104.55.0.0 | any | 10.3.3.31 | 1234 | Accept |
| 3 | TCP | 31.13.75.0 | any | 10.3.3.31 | 22 | Accept |
| 4 | TCP | 31.13.75.0 | any | 10.3.3.31 | 1234 | Accept |
| 5 | TCP | 23.63.9.0 | any | 10.3.3.31 | 22 | Accept |
| 6 | TCP | 23.63.9.0 | any | 10.3.3.31 | 1234 | Accept |
| 7 | TCP | 10.3.0.0 | any | 138.77.179.31 | 80 | Accept |
| 8 | TCP | 10.3.0.0 | any | 138.77.179.31 | 443 | Accept |
| 9 | TCP | 10.3.1.0 | any | 138.77.179.41 | 143 | Accept |
| 10 | TCP | 10.3.0.0 | any | any | 80 | Accept |
| 11 | TCP | 10.3.0.0 | any | any | 443 | Accept |
| 12 | TCP | any | any | 10.3.0.0 | any | Deny |
| 13 | TCP | any | any | 138.77.179.0 | 80 | Accept |
| 14 | TCP | any | any | 138.77.179.0 | 443 | Accept |
| 15 | TCP | any | any | 138.77.179.0 | 25 | Accept |
| 16 | any | any | any | any | any | Deny |
The regulation’s elaboration is given in the below table: –
| Regulation or rule no. | Elaboration |
| Rule : first and second | From the Research Professor’s home, these two Regulations recognize the “FTP” and “ssh” ports to link the Research subnet server to the ISP. |
| Rule : third and four | These two rules allow the “FTP” and “ssh” ports on the Research Subnet registry from Research Partner-1. |
| Rule : fifth and sixth | These two rules allow the “FTP” and “ssh” ports on the Research Subnet registry of the Research Partner-2. |
| Rule: seventh and eight | These two rules give the user access to the DMZ web server. |
| Rule: nine | This one provision entitles the Staff-subnet to the DMZ mail server. |
| Rule: ten and eleven | These two rules make it possible for any shared SUBNET user to have access to online websites. |
| Rule: twelve | This rule cancels the subnet link of the recipient. |
| Rule: thirteen, fourteen and fifteen | These guidelines Recognize multiple web users in order to provide access to the DMZ server. |
| Rule: sixteen | This one rule cancels traffic between the destination and the source site. |
Two rules allow the professor to have access to the device from his own home. These two rules would include an approved network link to the professor to access the network on the “VPN” to a specific Internet Protocol address. The professor can pass the documents to the other user by applying these guidelines, and the professor can share the file with other users who are present on a related sub-network. The firewall gates have been unlocked so that the professor can access the sub-network without any hassle. If the professor updates his IP address, there should be a continuity of the firewall. There must be a limitation that denies the access of unauthorized users through the “VPN or virtual private network.”
