Assignment- 2
Unit Coordinator: MMM
Tutor: RRR
Prepared By:
RR
NNN
Executive summary:
The report presents the successful process for the growth of a Smart Pharmacy organizational structure situated in Botany, NSW. SP is giving additional distributed products from franchises to customers. Clients are willing to accept innovative brands, medications, and commodities for the resource. Likewise, SP is effective in processing, where the products supplied are processed by suppliers. In Botany, NSW, they get their own factory. SP comprises one executive director, network manager, logistics manager, administrator, and data scientist. SP has an independent door-to-door distribution conveyance. They will get requests and are accountable for the order’s delivery. Where the user wishes to make a submission. They speak to the person who provides door-to-door delivery. The application is accepted by the franchises via a network related to it. At a certain point, the franchises collect the request from the customer and communicate it door-to-door to the delivery man.
The main objective of this research would be to set up the appropriate company that meets the organizational goals of SP. Accumulated business goals have been transferred to specialized goals and doubts have been created through specialized goals to organize the organization. All SP client channels, data store areas, webserver use, devices used, traffic patterns including applications, according to company goals. The QoS and convention used were scrambled off along with devices being utilized adequately referred to and labeled. All the details collected have been used as a guideline for a coherent overview. To associate the SP organization with the untouchables, by use of dual ISPs, one as a reinforcement ISP is important. The ISP-created VPN burrow allows secure data transmission. For any organizational structure, protection is the primary concern, therefore more focus has been placed on the implementation of safety indicators, the use of firewalls, mediators, NAT, and all SP workers in the DMZ are able to keep the structure in a secure state. To associate the SP organization with the untouchables, by use of dual ISPs, one as a reinforcement ISP is important. The ISP-created VPN burrow allows secure data transmission.
For any organizational structure, protection is the primary concern, therefore more focus has been placed on the implementation of safety indicators, the use of firewalls, mediators, NAT, and all SP workers in the DMZ are able to keep the structure in a secure state.
Table of Contents
2. Business Goals and Constraints. 5
3. Technical Goals and Trade-offs. 6
4. Table of User Communities, Data Stores, Network Applications and Traffic Flows. 8
5. Model for Addressing and Naming. 12
6. Explanation and Justification of the Logical Network Design. 15
7. Logical Network Diagram Including addressing and naming. 16
8. Routing and Switching Protocols. 18
11. The table of networking & communication devices and applications with price, quantity, and total cost:. 23
13. Test Plan for the network. 28
14. Detailed test script in the test plan. 29
Introduction
1.1 Project Goal
The basic goal of an organization is a secure, stable, and effective framework of the Smart Pharmacy (SP) network. The recommended system design could be protected and used efficiently and securely by SP clients and breeders with the use of the top-down approach. some of the stated objectives are:
- To interact with its stakeholders, SP must hold its network.
- Clients or sellers can access the information using their device about the goods and order inquiries.
- Payments by them can be made through a protected payment method using the SP Web Interface.
- Support to the franchise can be done by publishing their products into the market.
- With the help of SP network, Franchisees will access their devices.
- Customer will be able to ask for their specifications and SP should deliver their questions.
- Enable stakeholders to access the SP network and applications.
- Enable distribution personnel to use the SP network.
- The SP network must position properly and give excellent protection.
1.2 Project Scope
The scope of the projects shall determine the basic objectives, activities, objectives, achievement, requirements, outlines, expenditures as well as some parts of the reports. Expectations can be internal and external. The structure not seen by the end-user is merged with internal objectives. We should equip the organization for the physical and logical network diagram of the design and arrangement. Outer requirements include the part that is displayed on the side of the customer or user. Corporation security is able to translate all market needs into profoundly specialized necessities which include the integrity, customization, and responsiveness of the framework. In the setup field, the initial enlargement is the governance of the stable plan and IP distribution that tends to draw. Besides, it is based on the physical plan with test checking. In the setup field, the main extension is the governance of the stable schedule and IP distribution that tends to plan. Also, it is based on the physical plan with test validation.
2. Business Goals and Constraints
The business goals in an organization define what the organization is intended to achieve. Where the company will grow in competing for the environment by accomplishing the business goals. Moreover, setting goals is an effective strategy for the organization’s growth. Every corner of the business can be developed by using business goals. The following are the business goals for the Smart Pharmacy.
In development plans, organizations and companies such as Smart Pharmacy (SP) typically design their objectives and aspirations. Goals could usually be connected to the company, departments, members, customers, or another area of the company.
Business Goals
BG1: The Smart Pharmacy (SP) office, which is located at the warehouse will manage the whole organization’s operations. Those were including business operations, network operations, financial and sales operations.
BG2: As SP provides products and other health information to the franchise, there should be the real-time transmission of information from warehouse to franchise.
BG3: The business operations will be held all the time in a day. So, the network operator should be 24/7.
BG4: The delivery team must have access to the SP network from everywhere during the order delivery.
BG5: The customers can view the products online that are available at the different franchises. Also, they can do payments through the SP web interface securely.
BG6: Stock to the franchise is managed by a warehouse where the franchise must have access to the SP network.
BG7: Main people of the organization managing director, logistic manager, purchasing manager, account and finance manager, and others must have access to the SP and franchise network.
BG8: The servers and other devices, those placed in a warehouse secured by SP.
BG9: Enabling investors to connect the SP platform and implementations.
BG10: Make use of the SP network by distribution personnel.
Business Constraints
The business constraints are the factors those troubles the achievement of business goals. In the SP scenario, there are two business constraints. The first one is a problem with baking services. This will trouble the BG5, where the payments from the bank will be delayed in some cases. In addition, the delivery team operates outside the company network. Where they use the internet to connect company networks to get details about customer details, order details, and more. However, the signal strength in all places will not be equal. Hence, this troubles the BG4.
Competitors in the industry communicate with the organization’s goals but limit the rate of effectiveness. For each situation, door-to-door distribution happens in the different New south wales suburbs and utilizes mobile service to surf the content. The purchase period for line customers and approval time is crucial in this case. In assigned time and transaction policies, the shipment of the product to customers is indeed the major parameter of SP.
3. Technical Goals and Trade OFFs
The technical goals of the organization include factors like flexibility, protection, accessibility, and more. For Smart Pharmacy, the following are the technical goals.
Technical Goals (TG) is a specialized objective for every project that involves efficiency, usability, preparations for implementation, security, tolerance, comfort, versatility, and moderate. There are many trade-offs related to certain objectives that had their BG but according to BG a few of the TG are classified as:
Technical Goals
TG1: Use of dedicated devices for individual operations.
TG2: The organization needs to provide video streaming to the franchise to provide information about products and health information.
TG3: Using network devices and other devices to increase network availability.
TG4: Secure communication is needed between the organization and the delivery team.
TG5: The organization needs to provide a secure payment gateway.
TG6: The data transmission from SP warehouse to franchise and delivery team should be done in a secure way.
TG7: The SP should provide video stream from warehouse to franchise seamlessly.
TG8: The security of the servers placed in the office must be provided.
TG9: The user community experiences with the wearable mobile device users should be about BG10.
TG10: when using the SP networking system which uses Firewall, VPN tunneling & Proxy filtering both entities can interact via BG9.
Trade-offs
The technical objectives are scalability, flexibility, performance, availability, security, manageability, usability, affordability, and audibility. Trade-offs are aimed at targets of long-term and short-term. To accomplish device scalability, it is necessary to enhance the network site, improve the size of the client and network, and enhance the network server of SP. Trade-offs are the specific choices that batter one benefit to having another part. In this case, as per TG9, consumer networks that are using their computer from the outside system (could be mobile devices, for example, desktop computers, mobiles) should have access to the new system structure.
Trade-offs making:
| Availability | 35 |
| Scalability | 25 |
| Performance | 10 |
| Security | 10 |
| Management | 5 |
| Usability | 5 |
| Adaptability | 5 |
| Affordability | 5 |
| Total | 100 |
4. Table of User Communities, Data Stores, Network Applications and Traffic Flows
User Communities
| S. No | User community name | No of people in Community | Community Location |
| 1 | Managing Director | 1 | SP Office, Botany, NSW |
| 2 | Network Manager | 1 | SP Office, Botany, NSW |
| 3 | Logistic Manager | 1 | SP Office, Botany, NSW |
| 4 | Storekeeper | 1 | SP Office, Botany, NSW |
| 5 | Purchasing Manager | 1 | SP Office, Botany, NSW |
| 6 | Account and Finance Manager | 1 | SP Office, Botany, NSW |
| 7 | Customers | N/A | Anywhere in Australia |
| 8 | Manufacturers | 4 | All over the world |
| 9 | Delivery team | 20 | Anywhere in Australia |
| 10 | Franchise team | 10 | NSW, Australia |
Table1: user communities
Network Applications
| S. No | Network Applications | Application usages | User Communities |
| 1. | Inventory Handler | Purchasing Manager Logistic Manager Storekeeper | |
| 2. | Delivery Handler | Delivery team, Account and Finance manager, Customers | |
| 3. | Payment Handler | Customer, Account and Finance manager, and Manufacturer | |
| 4. | POS | Account and Finance Manager | |
| 5. | ERP | Managing director | |
| 6. | All user communities |
Table2: Network applications
Datastores
| S. No | Data Stores | Location | User Communities | Applications |
| 1. | Webserver | Botany NSW | All | Payment handler |
| 2. | Application server | Botany NSW | All | All applications |
| 3. | Database server | Botany NSW | All | All applications |
| 4. | Mail server | Botany NSW | All | |
| 5. | Video stream server | Botany NSW | All | ERP |
| 6. | DNS server | Botany NSW | Managing Director, Network Manager | All |
Table3: Datastores
Traffic Flows
All values are in kbps
| Data Stores | Managing Director | Logistic Manager | Data Analyst | Accountant | Purchasing Manager | Storekeeper | Network Manager |
| Web Server | 400kbps | 200kbps | 300kbps | 400kbps | 250kbps | 350kbps | 100kbps |
| Mail Server | 300kbps | 250kbps | 3500kbps | 250kbps | 350kbps | 250kbps | 350kbps |
| Database Server | 300kbps | 350kbps | 4500kbps | 3500kbps | 250kbps | 350kbps | 100kbps |
| Video Server | 300kbps | 350kbps | 350kbps | 200kbps | 100kbps | 250kbps | 350kbps |
| DNS | 150kbps | 200kbps | 200kbps | 100kbps | 350kbps | 350kbps | 150kbps |
| Application Server | 200kbps | 150kbps | 100kbps | 150kbps | 250kbps | 100kbps | 250kbps |
| Total Bandwidth | 20mbps |
Table4: traffic flow
Generally, in high point store hours, we will predict the Managing Director to be prepared to start 6-page boundaries of web sites at a moment. Unless the frequency distribution for 1 webpage is 50kbps, and at the peak office hours, the rate for functioning web becomes 300kbps. For system administrators and shop assistants, the same speed is assigned. MD can attach or deliver 2 emails at a time in most disastrous situations. If he requires 50kbps to send 1 email, he requires 100kbps to deliver 2 emails at that point. This is often believed to be enough for a particular workplace. Through the use of network capacity by the accounting firm, Logistic Manager, Purchasing Manager, and the user group is assigned as per their requirements mostly in the menu in the same scenario. If all department uses web maintenance, application, benefits at the peak work time, it is decided that 20mbps frequency is appropriate for the SP to coordinate. The leased line with something like a bandwidth of 20mbps from ISP would be linked to the SP enterprise system.
5. Model for Addressing and Naming
Naming
| S. No | Network Components and Services | Given Name |
| 1 | Managing Director Computer | PCMd |
| 2 | Network Manager Computer | PCNm |
| 3 | Logistic Manager Computer | PCLm |
| 4 | Storekeeper Computer | PCSk |
| 5 | Purchasing Manager | PCPm |
| 6 | Franchise Computer | PCFc |
| 7 | Account and Finance Manager Computer | PCAFm |
| 8 | Delivery team handphone | HpDt |
| 9 | Switch | Swt |
| 10 | Router | Rtr |
| 11 | Firewall | FW |
| 12 | Demilitarized Zone | DMZ |
| 13 | Dynamic Host Configuration Protocol | DHCP |
| 14 | Network Address Translator | NAT |
| 15 | Virtual LAN | VLAN |
| 16 | Webserver | WebSvr |
| 17 | Application Server | AppSvr |
| 18 | Database Server | DbSvr |
| 19 | Mail Server | MailSvr |
| 20 | Video Server | VdSvr |
| 21 | Domain Name System Server | DNSSvr |
Table 5: Naming
5 Addressing
There is a smaller number of IP addresses required for the Smart Pharmacy network. The network has devices less than 35. Hence, class C was chosen to allocate addresses. The network bit 27 will give the 32 addresses which were sufficient for SP network. This will avoid wastages of ip addresses.
Smart Pharmacy Network:
Number of users and devices: Not more than 32 according to the analysis
Subnet address: Class C with /27: 192.168.1.0/27
Gateway address: 192.168.1.1
The number of hosts that can be allocated apart from network and broadcast is 32-2 =30
| Computers | Allocation Type | Subnet | Subnet Mask | Gateway |
| PCMd | DHCP | 192.168.1.0 | 255.255.255.224 | 192.168.1.1 |
| PCNm | DHCP | 192.168.1.0 | 255.255.255.224 | 192.168.1.1 |
| PCLm | DHCP | 192.168.1.0 | 255.255.255.224 | 192.168.1.1 |
| PCSk | DHCP | 192.168.1.0 | 255.255.255.224 | 192.168.1.1 |
| PCPm | DHCP | 192.168.1.0 | 255.255.255.224 | 192.168.1.1 |
| PCFc | DHCP | 192.168.1.0 | 255.255.255.224 | 192.168.1.1 |
| PCAFm | DHCP | 192.168.1.0 | 255.255.255.224 | 192.168.1.1 |
Table6: Addressing 1
Servers:
The SP servers were placed inside the DMZ for security purpose. Also, public ip address was allocated for the DMZ. Moreover, the firewall also used to provide more security. The servers are less than 20. Hence, mask /28 taken to have 16 addresses. Where 14 can be used for hosts. The servers in DMZ are Webserver, Application server, Mail server, DNS server, Database server, Video server.
Subnet address: 172.16.1.0/28
Gateway address: 172.16.1.1/28
| Sever | Allocation type | Address | Mask | Gateway |
| WebSvr | Static | 172.16.1.2 | 255.255.255.240 | 172.16.1.1 |
| AppSvr | Static | 172.16.1.3 | 255.255.255.240 | 172.16.1.1 |
| DbSvr | Static | 172.16.1.4 | 255.255.255.240 | 172.16.1.1 |
| MailSvr | Static | 172.16.1.5 | 255.255.255.240 | 172.16.1.1 |
| VdSvr | Static | 172.16.1.6 | 255.255.255.240 | 172.16.1.1 |
| DNSSvr | Static | 172.16.1.7 | 255.255.255.240 | 172.16.1.1 |
Table 7: addressing for server
6. Explanation and Justification of the Logical Network Design
- The SP office can perform all operations those related to importing goods, sending stocks, online purchase, delivery and more by using applications mentioned above-BG1
- The SP office uses Video Streaming server to provide information about the products and other health information. – BG2
- The SP providing all time access to the network. Where users can connect by using local network to get remote internet access and to access configured SP. – BG3
- The delivery team, customers, franchise uses the ISP access points and VPN tunnel to share and connect to network securely from anywhere. – BG4, BG5, BG6, BG8
- The PC’s of main people in the organisation managing director, logistic manager, purchasing manager, network manager, account and finance manager, storekeeper were enabled with VoIP and DHCP IP addresses. – BG7
- Complete SP network using in-house software and applications to provide various business services. Also, using backup to avoid data loss. – TG1
- The video server that placed inside DMZ provides streaming services to the various franchise securely. – TG2
- There is a backup taken for network where the services can be run for 24/7. – TG3
- The communication and transfer of information between and within organisation achieved through DMZ, VPN, and firewall. – TG4, TG5, TG6
- There is a video server that placed inside DMZ to secure. This server enables the office to check streaming of video at franchise. Hence, the office can control the problems in streaming. – TG7
- The DMZ placed in the network will provide secure zone to the organisation servers. – TG8
7. Logical Network Diagram Including addressing and naming

8. Routing and Switching Protocols
Routing Protocols
VLAN Trunk Protocol used for network inclusion, VLAN power, and termination. It makes the bridge between the switches. In the Smart Pharmacy scenario, there we used the default route to connect to the ISP switch. Where one another which used for VLAN which does not inbuilt guiding convention.
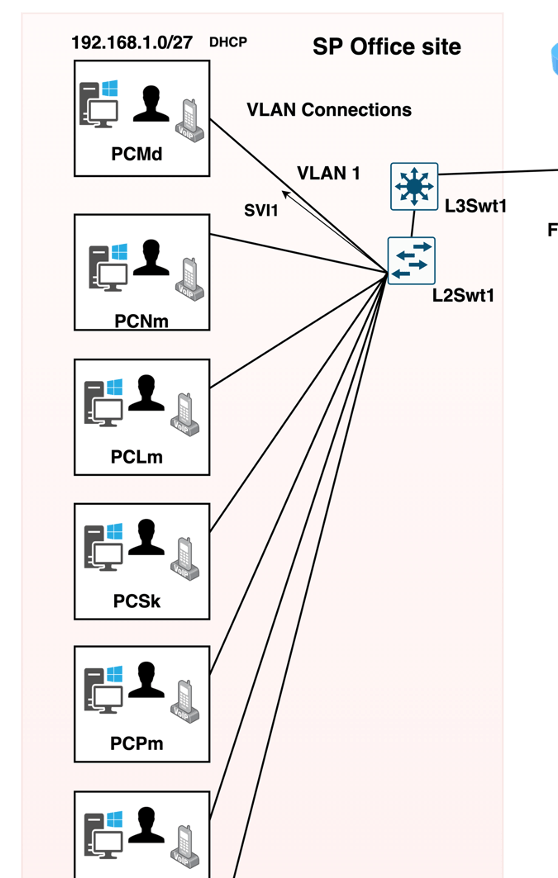
The subnet taken for the SP office is 192.168.1.0/27. The routing from the office users to the router will happen through a VLAN connection. For example, if it is assumed that all users in the SP belong to one VLAN, then the routing will follow like below:
Network address: 192.168.1.0
Subnet mask: /27
Next hop address: 192.168.0.5/27
Also, the default route will happen through the next-hop address 192.168.0.1/27 with network 0.0.0.0 by using the default mask.
Switching protocols
In the SP scenario, there were two layer2 switches and two layer3 switches were used. Those are L2Swt1, L2Swt2, L3Swt1, L3Swt2. The exchanging convention may avoid by L2Swt2 and L3Swt2 as they are kept in a discreet place. The L2Swt1 and L3Swt1 were used for distinctive exchange conventions. Where it ensures effective and efficient transfer of information.
Open Shortest Path First
It is an inside passage convention that relies on the ingenuity of the interface state that is used to transfer the data inside a solitary self-ruling structure. Instead of updating the entire directory table, OSPF preferably merges its organization as it communicates Link-state routing. Link-state algorithm is modified where every switch produces the same connection state knowledge base so that the most restricted way to achieve the target can be built and figured out. OSPF is also broadly transmitted these days as an open standard. OSPF is also aimed at conquering the disadvantages of the previous convention, increasing flexibility, and making it faster.
Border Gateway Protocol(BGP)
BGP can be defined as a normalized Exterior Gateway Protocol (EGP) variant that follows the convention of vector steering. It is used to transfer the parcels, between the self-sufficient framework, via the web. BGP offers reliability, adaptability, and flexibility to the network. Regardless of any ruined web way, it guarantees parcel compasses to the target, regularly selects the way for directions made by the organization’s leader, holds up a regular steering table, and updates the tables at some point a few adjustments occur. The geography of a customer worker is used to communicate between the customer and the worker that relies on the TCP / IP to trade the steering data
Spanning Tree Protocol
The Spanning Tree Protocol is used for layer 2 switching. The primary function of the STP is the root link. By using this, the most efficient route to the central switch will be identified.
In addition, this protocol ensures the pre-empt of circles. This protocol works based on IEEE 802.1D. There will be no Bridge Protocol Data Units sent when there is an own BPDU returned. Otherwise, the switches will send BPDU to determine circles.
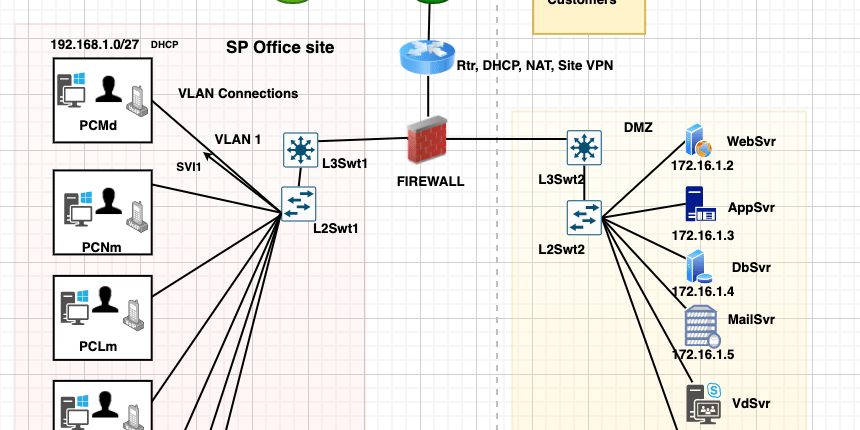
Layer 2 and layer 3, for the communication, the spanning over the tree will be applied. This will handle the MAC and reduce the need. For the SP network, the L3Swt1 will be the center switch. The virtual LANs use dedicated virtual switch interfaces for transferring information. The virtual switch interface plan will identify the shortest path to link the VLAN. The image below shows an example of a virtual switch interface to the individual VLAN.
9. Security Mechanisms
OSI layer represents the security mechanisms that are mentioned in the SP system. protection mechanisms are addressed in each OSI layer.
- Physical layer: In the physical layer single process is on hold to make sure that the device will be accessible even after the dissatisfaction in the power. The systems in the physical layer placed in the framework and the interface of the security are applied on each occasion of cat 6. The security strategies are based on wiring, cabling, and physical devices.
- Datalink layer: This is the second layer; it contains the security mechanisms. By using the Access control lists MAC isolation is implemented. VLANs must prepare to provide protection in the same manner.
- Network layer: For processing the IP, the access control list is used. IPsec is also used for the protection of the IPs.
- Transport layer: SP switch contains the firewall built-in system for the intersection of the contaminated information from external resources to assure the elements in the transportation layer. Various security examples are TLS, SSH, SSL.
- session layer: There are seven business departments in the Botany, which will separate as individual passwords from the PCs. Outside customers system transmission must be constrained access to the operators.
- presentation layer: To communicate among the user systems, AES uses the unscrambling and encrypted configurations.
- Application layer: To provide the protection it uses the HTTPS server. In the web application, security mechanisms are approved on the website applications.
- User security layer: At the user level, the security will be two-factor approval. The secured sites and encryption, email, folder, and genius confirmation
10.Physical Diagram

11. The table of networking & communication devices and applications with price, quantity, and total cost:
11.1 Device Cost
| S. No | Devices | Product Number | Quantity | Unit Price | Cost |
| 1. | Computer | ThinkStation P330 | 8 | $1000.00 | $8000.00 |
| 2. | Monitor | Dell 24 Monitor – S2421HN | 8 | $200 | $1600.00 |
| 3. | Switch (Layer3) | S5500-48gt4gf | 2 | $1500 | $3000.00 |
| 4. | Switch (Layer2) | WS-C2960-24TT-L | 2 | $ 400 | $800.00 |
| 5. | Router | Cisco RV320 | 1 | $800.00 | $800.00 |
| 6. | Firewall | Fortinet FortiGate 30 e | 1 | $800.00 | $800.00 |
| 7. | Server | Rack Server Think System SR650 | 6 | $1500.00 | $9000.00 |
| 8. | Portable device | Samsung, tablet | 12 | $1200 | $14400.00 |
| 9. | VOIP Telephone | Cisco CP-8861 | 4 | $100 | $400.00 |
| 10. | Fibre Optical Cable | Toslink Optical Cable | 500m | $20 | $1000.00 |
| 11. | Copper wire | Cat 7 | 500m | $10 | $500.00 |
| 12. | Networking tools | RJ45 | – | $800.00 | |
| 13. | the installation cost for ISP | Telstra or/and Optus | – | – | $10000.00 |
| Total Cost | $61020.00 |
11.2 Application Cost
| S. No | Application | Version/ Software | Cost/yearly |
| 1. | Inventory Handler | Granular | $1700.00 |
| 2. | Payment Handler | Blender | $1500.00 |
| 3. | Delivery Handler | Scurri | $2000.00 |
| 4. | ERP | SAP ERP 3.7 | $1800.00 |
| 5. | Database | Microsoft SQL | $300 |
| 6. | Gmail | $1500.00 | |
| 7. | Browser | Chrome | $800.00 |
| 8. | POS | Vend | $200 |
| Total Cost | $8900/yearly |
12. The explanation and justification of the networking & communication devices and applications required
| S. No | Business goal | Options with their specification (device, software, tools, equipment) | Selected device Justification |
| 1. | BG1: The Smart Pharmacy (SP) office, which is located at the warehouse will manage the whole organization’s operations. Those were including business operations, network operations, financial and sales operations. | Inventory Handler (Granular) Payment Handler (Blender) Delivery Handler (Scurri) SAP ERP 3.7 Database (Microsoft SQL) Email, Gmail Browser (Chrome) POS (Vend) | All these applications were selected by considering the different factors cost, effectiveness, performance, adaptability, etc. |
| 2. | BG2: As SP provides products and other health information to the franchise, there should be the real-time transmission of information from warehouse to franchise. | Microsoft SQLRack Server Think System SR650 | – Microsoft SQL is a widely chosen solution for databases in recent years. The data storage, access, modification, and other functionality are very simple and easy in Microsoft SQL – The video server is used for transmitting continuous streaming and videos to the franchise. |
| 3. | The business operations will be held all the time in a day. So, the network operator should be 24/7. | ISP-Optus Backup Service (Telstra) | We have selected Optus service for maximum internet services. Also backup service Telstra was chosen as a backup for use at drop-off. |
| 4. | The delivery team must have access to the SP network from everywhere during the order delivery. | Portable devices phone, tablet | The portable devices were chosen as iPhone Max and tablet. Where these devices will have high-end performance and high memory. |
| 5. | The customers can view the products online that are available at the different franchises. Also, they can do payments through SP web interface securely. | Rack Server Think System SR650Payment Handler (Blender)Microsoft SQL | The Think System SR570 is chosen for quality and performance. As there is an online site, the performance of the server must be high. Blender is one of the ways for processing the payments. This offers security to the information that processing. Microsoft SQL is a widely chosen solution for databases in recent years. The data storage, access, modification, and other functionality are very simple and easy in Microsoft SQL |
| 6. | Stock to the franchise is managed by a warehouse where the franchise must have access to the SP network. | VPN | There is site-to-site connectivity from the franchise to the warehouse. Where the VPN provides secure communication between franchisee and site |
| 7. | Main people of organization managing director, logistic manager, purchasing manager, account and finance manager, and others must have access to the SP and franchise network. | Desktop Pc ThinkStation P330 L2Switches WS-C2960-24TT-L L3Swithces S5500-48gt4gf | All these applications were selected by considering the different factors cost, effectiveness, performance, adaptability, etc |
13. Test Plan for the network
To indicate if the uniform framework works correctly, we must have various tests. Such evaluations will have to meet the aims of the organization. Plan proposals for the verification of coordinates within the corresponding point:
The main task to be completed is checking the number of remarkable organizations that are implemented by the ISP. The organizations in the SP and ISP must have been followed. The main standards that must be evaluated are the application limit and site speed of the organization’s implementation.
Security Testing:
To preserve the layout in mode, confirmation throughout the full day will be regarded at every rate. Protection must be addressed to the degree that firewalls, virus protection, authentication models, like SSL, possible invader identification, and framework programming execution are used.
Volume Testing:
Besides, SP must acknowledge the growing and emerging threats and possible weaknesses inside the framework. Decreased authentication protocol framework/clients, tools, and implementation ratios must be defined by the confirmation principle of course events.
Recovery Testing:
Recovery Research is approved to decide if SP operations can be well conducted throughout the wake of data loss, cataclysm, or credibility inside the device. With this personalized evaluation, retrieving the system from any possibility of extortion is the critical mission. Defenses and relevant reports with this SP must be made.
Thread Testing:
Thread report is done at the outset of the connectivity evaluation process. Technical abilities in any activity can be calculated from that kind of examination. In SP, two kinds of thread verification are performed. Each code is being swapped for impact, is remembered by single thread test results, and multi-thread validation unifies so many simultaneous interactions in a stepwise manner.
Database integrity testing:
The large variety of loops, procedures and processes used in analyzing, updating, and bringing to many data sets will be calculated by measuring the righteousness of the skill set. This research position would be helpful to have the desired yield across the accuracy and reliability of all the data set aside. SP must be keen on the data elements of ACIDs.
Function Testing:
Application testing will be carried out as a significant element of sample checking. This sample analysis is helpful because of the incredible number of contraptions per segment. With its valid utility, unambiguous regulation of the system is attempted. The SP structure and process should be associated with conspicuous proof of contraptions and programming with their standard results, investigating arranged and real yields.
14. Detailed test script in test plan
To gain access to the web and video server located in the DMZ in Botany NSW from the Managing Director PC (PCMd).
Test Objectives:
The application from the Managing Director PC (PCMd) should be recognized by a firewall established in the Botany Office and forwarded to the video worker. The requests sent from the customer gadget and portable devices to the two servers may get rejected by the same firewall.
Test Steps:
A set of firewall rules are arranged in the Firewall.
Regulations:
- Enable requests to the Video Server from the Managing Director PC (PCMd).
- Enable requests to the Web Server from the Managing Director PC (PCMd) and accept them.
- To reject and decline Web Server Customer Gadget requests.
- Reject and deny Video Server requests from the Customer Gadget requests.
Testing:
It should be possible to review firewall strategy by sending Ping requests from Managing Director PC (PCMd) and client gadgets.
- The Ping request is sent from PCMd to the Web server’s IP address.
- Ping request to the video server’s IP address sent from the PCMd.
- Ping request to the IP address of the Video Server sent from the Customer Gadget.
- Ping request sent from the Customer Gadget to the Web server’s IP address.
Observation:
The firewall strategy perception is accomplished after delivering the Ping request.
- From the video and web servers, PCMD receives a ping response with 0% loss.
- From the video and web servers, customer gadget receives a ping response with statistics loss of 100%.
Managing Director PC (PCMD) and the firewall policy for Video and Web Servers are established in the firewall. It supports the entry of the Managing Director PC (PCM) to the DMZ zone. The request of PCMD is answered by Video and Web Server, but the strategy of firewall declines the admissions of client gadgets to the DMZ region. And the gadget request was not replied to by the Video and the Web Servers. So, we can assume that in the design of the firewall, the agreement decides that we have performed for us.
15. Conclusion
The focus of this report is the organizational strategy that has been established as well as the related process of configuration strategy executed to construct the organization’s physical and logical network architecture. The company’s objectives, scope, business requirements, and specific goals were identified while organizing rational arrangements. We had the choice to construct the shrewd structure shown by the objectives.
The tables, database plans, and information sources for local distribution networks by user groups were analyzed and confirmed as appropriate. The IP and the naming of the device were completed. The right intellectual plan and practical plan were implemented and promoted with consistency. The hardware utilized has been demonstrated and extensive details showed the expense of every piece of equipment. Likewise, the research plans were recorded and the following methodology for the testing process was done. This study concludes by describing, publishing all the methods and processes had to develop a coherent plan for every framework but further demonstrating the application of that simple level executives to change it think about all assumptions and objectives in the physical plan.
References
Oppenheimer, P. (2011), Top-Down Network Design, Third Edition, Cisco. Press, Indianapolis [Accessed 4 Oct. 2017].
Mitchell, B 2017, ”DMZ-De- Militarized Zone (Computer Networking)”, viewed 2020/05/05.
Ash, H 2018, “ What is logical network diagram?”, viewed 2020/03/20, https://graphicalnetworks.com/blog-what-is-a-logical-network-diagram/
https://www.lifewire.com/demilitarized-zone- computer-networking- 816407
Simmons, M 2011,” Logical Network Layout for Small Networks”, viewed 2020/05/24,
Rouse, M 2018, DMZ (networking), viewed 2020/10/05, https://searchsecurity.techtarget.com/definition/DMZ
Li, H 2016,” Network topology design”, viewed 2020/05/29, https://www.sciencedirect.com/topics/computer-science/network-topology-designdf
